Kevi "Fauda" Agit, Kurdish explosive expert and new Merc in JA3. Her character looks great, we are yet to hear her voice. As pointed by a fan, the flag in her bio
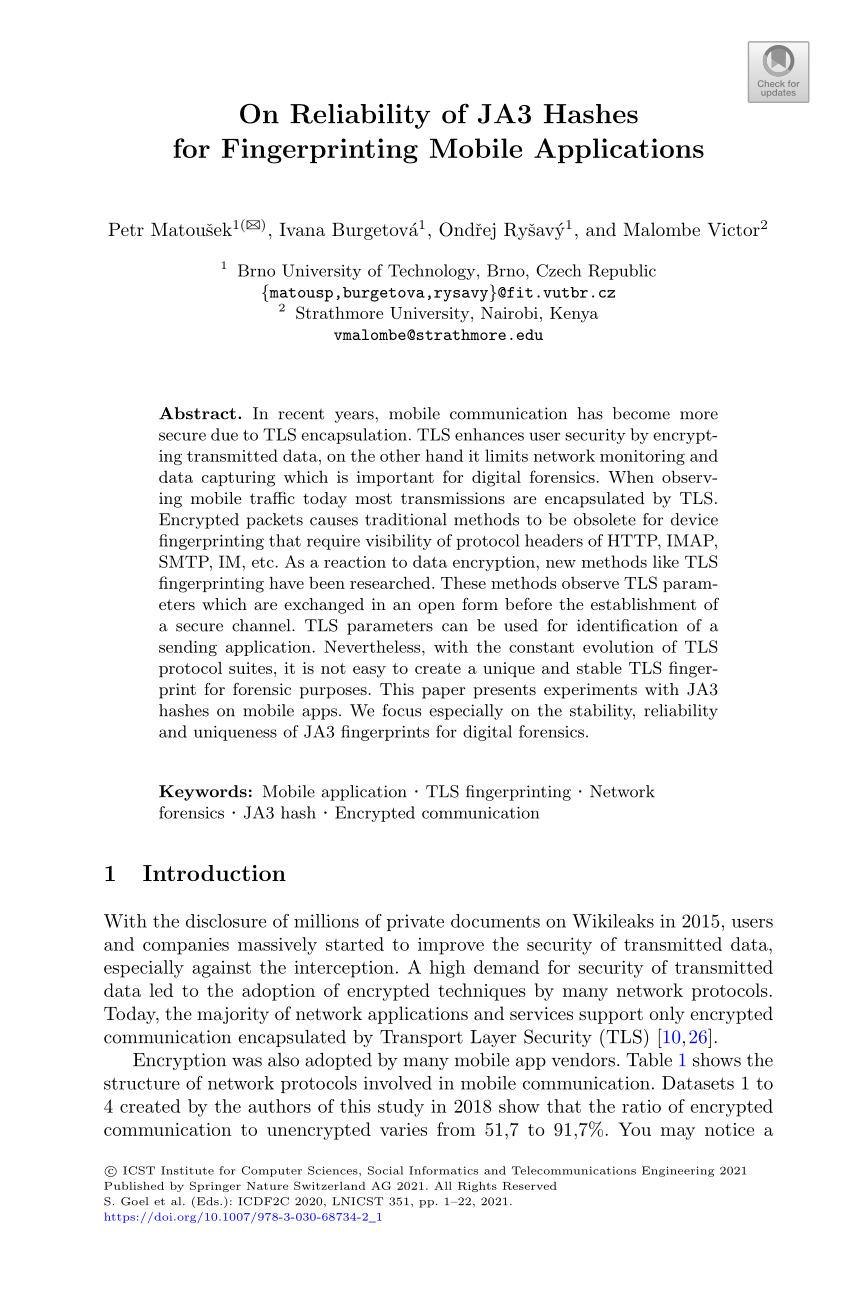
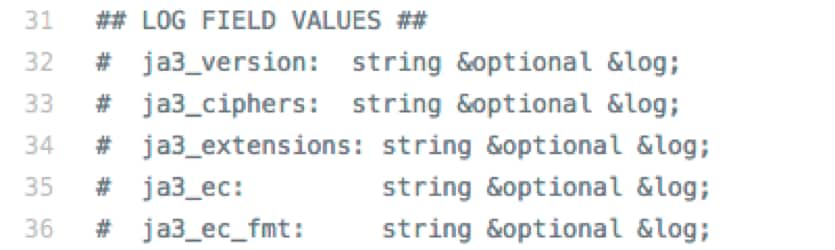
GitHub - matousp/ja3s-fingerprinting: Scripts for fingerprinting mobile apps using JA3 and JA3S hashes.
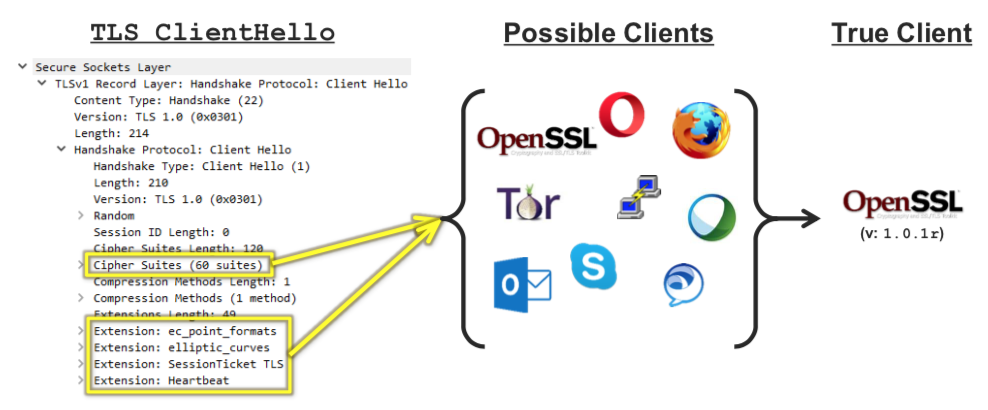
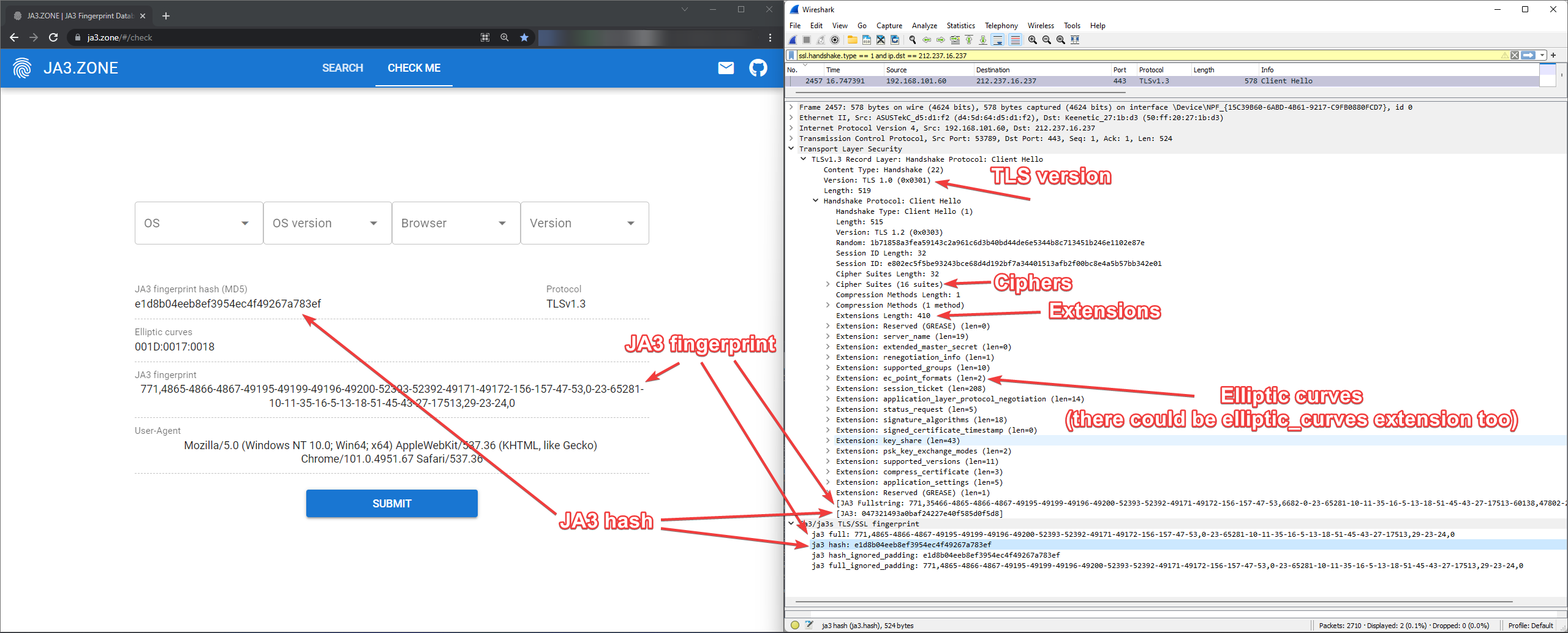
GitHub - salesforce/ja3: JA3 is a standard for creating SSL client fingerprints in an easy to produce and shareable way.